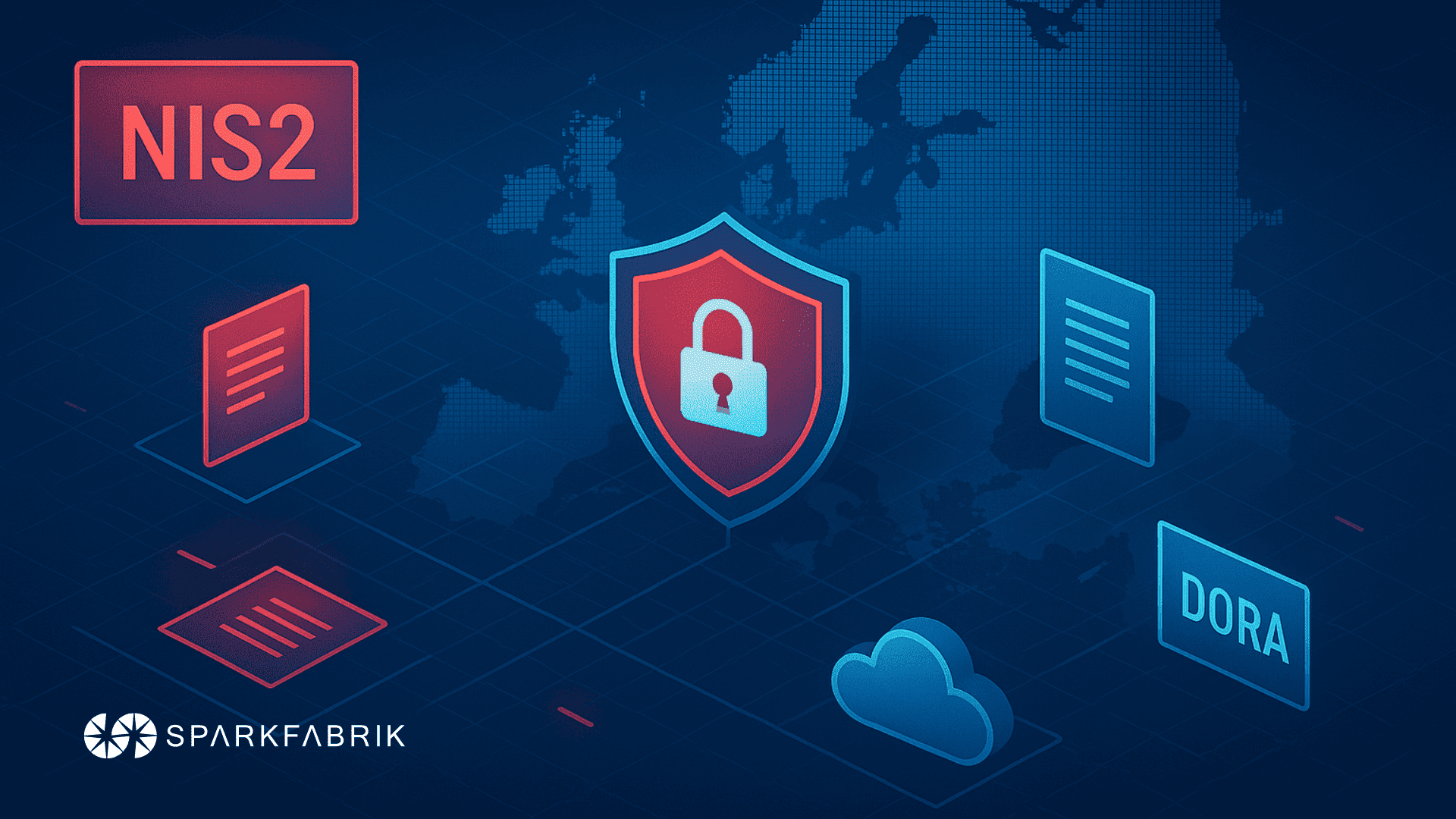
Software supply chain security has become a priority for businesses — or at least it should be. According to the 2024 Report on ICT Security in Italy by CLUSIT, cyber attacks have increased significantly.
Globally, an 11% increase was recorded, while in Italy the rise was even more concerning, reaching 65% in 2023 alone. This risk landscape is worsened by geopolitical conflicts, inflation, and economic instability, which push organizations to cut investments — including those in cybersecurity — to maintain a conservative financial position.
However, the need to strengthen supply chain security is increasingly evident. The SolarWinds attack of December 2020, which potentially involved 300,000 companies in the supply chain, is just one of many examples that highlighted how critical the issue of supply chain security really is.
In this article, we address the topic of software supply chain security, which was also at the center of the event “Talks on my Machine” organized by SparkFabrik on July 16, 2024. During the event, we explored common vulnerabilities, mitigation strategies, and best practices to strengthen supply chain security. But before diving into the topics covered by the experts, let’s take a step back.
What is supply chain security?
Let’s start with a definition. Supply chain security refers to the security of the entire software development process, from the initial design phases to final distribution, ensuring that every component and every phase is reliable. This concept is essential to ensure that every element of a piece of software, whether it is source code or a third-party library, is secure and free from vulnerabilities that could be exploited by malicious actors.
The risks associated with the software supply chain are numerous. Companies expose themselves to potential supply chain attacks when they fail to adequately control the origins of the components they use, risking the insertion of malicious code or critical vulnerabilities. Such compromises can lead to serious consequences, including loss of sensitive data, reputational damage, and operational disruptions. Therefore, supply chain security is not just a component of cybersecurity, but a fundamental pillar for safeguarding the integrity and reliability of the entire corporate software ecosystem.
YOU MIGHT ALSO BE INTERESTED IN:
- Software Supply Chain: what is it and what are its vulnerabilities?
- SBOM: the key to software security in the supply chain
Why is supply chain security important?
Supply chain security has become fundamentally important, as demonstrated by well-known attacks, including the aforementioned SolarWinds attack, or the Codecov incident in 2021. In this security incident, attackers compromised a development tool used for code analysis, altering it to exfiltrate sensitive data from the development environments of the companies that used it. This attack highlighted how crucial it is to constantly monitor and verify the integrity of the tools and software components in use.
Today, vulnerabilities are on the rise due to the growing complexity of modern software and the widespread use of third-party components. Developers often integrate external libraries and modules to speed up development timelines, but this introduces potential weak points. Furthermore, cybercriminals have identified the supply chain as a strategic target, exploiting the broad access it can provide to target systems. Consequently, companies must adopt proactive measures for supply chain security — implementing rigorous security controls, performing continuous verification, and constantly monitoring suppliers to protect systems and reduce the risk of attacks that could compromise the integrity and trust in distributed software.
READ ALSO:
- Software Security: best practices for security
- The Cyber Resilience Act, European competitiveness, and EU digital sovereignty
Deep dive into our cloud infrastructure supply chain
Deep dive nella supply chain della nostra infrastruttura cloud - Paolo Mainardi @ IDI 2023
Supply chain security best practices
We’ve now understood that software supply chain security is fundamental to protecting businesses from growing cyber threats. Using open source techniques and tools can help mitigate these risks effectively. Let’s look at some supply chain security best practices that can prove useful.
1 - Digital signature verification
Digital signature verification is a key practice for ensuring the authenticity and integrity of downloaded software. Tools like GnuPG (Gnu Privacy Guard) allow you to verify that software packages have been released by trusted sources and have not been tampered with along the distribution chain. This process ensures that only digitally signed and verified software can be installed and executed on corporate systems, reducing the risk of installing malicious software.
2 - Static and dynamic code analysis
Tools like SonarQube and OWASP Dependency-Check enable automated checks on software components and source code to identify known vulnerabilities and potential security risks. Integrating these analyses into the software development lifecycle helps identify and resolve security issues early, reducing the risk of compromise through software vulnerabilities.
3 - Least privilege controls
Implementing the principle of least privilege is always a winning strategy in cybersecurity. In the case of supply chain security as well, it is essential to limit privileged access only to critical and authorized components of the software supply chain. Tools like Docker and Kubernetes allow you to define and enforce strict access and authorization controls for resources and services, thereby reducing the attack surface and protecting sensitive data and configurations.
4 - Continuous security monitoring
Finally, continuous security monitoring is essential for promptly identifying and responding to threats against the software supply chain. Tools like Prometheus and Grafana allow you to collect and analyze security metrics in real time, detecting anomalies and suspicious behaviors that could indicate an attack or compromise.
But there is an even more effective way to prevent risks associated with software supply chain security: listening to the experts on the topic.
Talks on my Machine: Software Supply Chain Security
We have now understood that software supply chain security is a hot topic that deserves special attention. The online event by SparkFabrik offered essential insights for businesses and industry professionals. Experts shared their knowledge on various aspects of supply chain security. Watch the talks to discover advanced tools and innovative techniques to enhance supply chain security.
Supply chain security: a sandwich that goes well with GUAC
Supply chain security: a sandwich that goes well with GUAC - Michael Lieberman
Michael Lieberman, Co-founder and CTO of Kusari, in this talk shows us how both software producers and consumers play a crucial role in ensuring security. Discover the cutting-edge tools and practices that are transforming the industry, and how the GUAC project is improving transparency and observability in the software supply chain.
Building a reliable and resilient software supply chain
Costruire una supply chain di software affidabile e resiliente - Paolo Mainardi
Paolo Mainardi, Co-founder and CTO of SparkFabrik, provides an overview of the current state of the software supply chain, with a focus on significant events such as SolarWinds and log4shell. Topics covered in this talk include: emerging threats and mitigation strategies, including tools like Sigstore, Syft, and Grype to improve integrity and achieve unprecedented visibility into our artifacts and cloud infrastructures. Discover how these tools can help build a truly reliable and resilient software supply chain.
Protecting Terraform-based infrastructure as code from threats
Proteggere l’infrastruttura basata su codice Terraform dalle minacce - Andrea Panisson
Andrea Panisson, Cloud-Native Engineer at SparkFabrik, guides us through protecting infrastructures managed via Terraform, one of the most powerful Infrastructure as Code tools. Panisson illustrates the risks associated with using extended Terraform providers and modules, demonstrating some of the most common attacks and offering practical suggestions for mitigating them. Learn more about Terraform’s internal mechanisms and potential vulnerabilities in its supply chain.
Implementing Security with Kyverno on Kubernetes
Implementazione della Sicurezza con Kyverno su Kubernetes - Giuseppe Arancio
In this talk, Giuseppe Arancio, Cloud-Native Engineer at SparkFabrik, introduces Kyverno, an open source policy engine for Kubernetes that facilitates the implementation of security and compliance policies. Arancio shows us how to use Kyverno to validate OCI images, generate SBOMs, and integrate with CI/CD pipelines, creating a secure and automated workflow. And to wrap up: an overview of alternatives to Kyverno, providing a complete picture of the solutions that enable implementing a secure supply chain on Kubernetes.
In conclusion
In a context of growing cyber insecurity, businesses must view cybersecurity not just as an operational necessity, but as a strategic investment to mitigate risks and protect their business. Strengthening software supply chain security is essential to prepare your company for future challenges and ensure the integrity and reliability of the entire corporate software ecosystem.
Listening to experts, such as the speakers at “Talks on my Machine,” represents the first step toward a new strategic dimension of security.